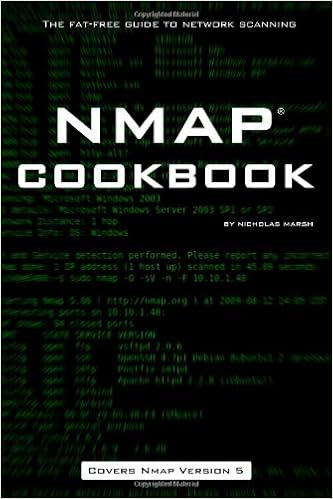
By Nicholas Marsh
Nmap(r) Cookbook: The fat-free advisor to community scanning presents simplified insurance of community scanning gains to be had within the Nmap suite of utilities. each Nmap characteristic is roofed with visible examples that will help you fast comprehend and determine right utilization for functional effects. issues lined comprise:
* set up on home windows, Mac OS X, Unix/Linux structures
* simple and complex scanning strategies
* community stock and defense auditing
* Firewall evasion strategies
* Zenmap - A graphical front-end for Nmap
* NSE - The Nmap Scripting Engine
* Ndiff - A Nmap experiment comparability software Simplified insurance of Nmap 5.00 positive aspects.
Read or Download Nmap Cookbook: The Fat-free Guide to Network Scanning PDF
Similar security books
Filenote: mobi produced from retail epub utilizing cloudconvert. org
------------
Good good recommendation and nice concepts in getting ready for and passing the qualified details platforms defense specialist administration (CISSP-ISSMP) examination, getting interviews and touchdown the qualified details platforms defense expert administration (CISSP-ISSMP) task. when you've got ready for the qualified info structures safeguard specialist administration (CISSP-ISSMP) examination - now's the instant to get this e-book and get ready for passing the examination and the way to discover and land a qualified info structures protection specialist administration (CISSP-ISSMP) activity, there's totally not anything that isn't completely lined within the e-book.
It is simple, and does a very good activity of explaining a few complicated issues. there's no cause to speculate in the other fabrics to discover and land a qualified info platforms defense expert administration (CISSP-ISSMP) qualified activity. The plan is lovely basic, purchase this booklet, learn it, do the perform questions, get the job.
This e-book figures out how one can boil down severe examination and task touchdown ideas into genuine international functions and situations. Which makes this publication effortless, interactive, and important as a source lengthy after scholars move the examination. those that educate qualified details platforms defense expert administration (CISSP-ISSMP) periods for a dwelling or for his or her businesses comprehend the real price of this booklet. you definitely will too.
To organize for the examination this ebook tells you:
- What you want to learn about the qualified info structures safety expert administration (CISSP-ISSMP) Certification and exam
- instruction guidance for passing the qualified details platforms defense specialist administration (CISSP-ISSMP) Certification Exam
- Taking tests
The ebook includes a number of feedback on how getting ready your self for an interview. this is often a facet that many of us underestimate, when having a well-written CV, a private weblog, and probably a few earlier tasks is definitively very important - there's even more to organize for. It covers non-technical features (how to discover a task, resume, behavioral and so on. ). A 'Must-study' earlier than taking a Tech Interview.
To Land the activity, it can provide the hands-on and how-to’s perception on
- discovering possibilities - the simplest locations to discover them
- Writing Unbeatable Resumes and canopy Letters
- Acing the Interview
- what to anticipate From Recruiters
- How employers hunt for Job-hunters. .. . and More
This booklet bargains first-class, insightful recommendation for everybody from entry-level to senior pros. not one of the different such profession publications evaluate with this one.
It sticks out simply because it:
- Explains how the folks doing the hiring imagine, that you can win them over on paper after which on your interview
- is stuffed with priceless work-sheets
- Explains each step of the job-hunting approach - from little-known methods for locating openings to getting forward at the job
This booklet covers every thing. even if you try to get your first qualified info structures defense specialist administration (CISSP-ISSMP) task or circulation up within the process, you may be completely happy you were given this book.
For any IT specialist who aspires to land a professional info platforms defense expert administration (CISSP-ISSMP) qualified task at best tech businesses, the foremost abilities which are an absolute should have are having an organization grab on qualified details platforms safety expert administration (CISSP-ISSMP) This ebook isn't just a compendium of most vital subject matters to your qualified info platforms protection expert administration (CISSP-ISSMP) examination and the way to move it, it additionally offers an interviewer's point of view and it covers features like smooth talents that the majority IT execs forget about or are ignorant of, and this e-book definitely is helping patch them.
When in the event you get this e-book? no matter if you're looking for a task or no longer, the answer's now.
Peer-To-Peer Storage: Security and Protocols
Peer-to-peer (P2P) has confirmed as a so much profitable method to produce huge scale, trustworthy, and good value functions, as illustrated for dossier sharing or VoIP. P2P garage is an rising box of software which permits friends to jointly leverage their assets in the direction of making sure the reliability and availability of consumer information.
This quantity gathers the papers offered at 3 workshops which are embedded within the IFIP/Sec convention in 2004, to enlighten particular issues which are at present rather lively in defense. the 1st one is the tenth IFIP Annual operating convention on info defense administration. it's equipped through the IFIP WG eleven.
- Hacking Interdit
- The Supply Side of Security: A Market Theory of Military Alliances
- State Recognition and Democratization in Sub-Saharan Africa: A New Dawn for Traditional Authorities? (Governance, Security and Development) 1st edition by Buur, Lars, Kyed, Helene Maria (2007) Hardcover
- Water and Food Security in Central Asia
Extra info for Nmap Cookbook: The Fat-free Guide to Network Scanning
Example text
But some asymmetric wars drag on well beyond what was anticipated before the fight. If power implies victory, and a lot of power implies quick and decisive victory, what then explains why power causes quick and decisive victory sometimes but not others? My answer is strategy. The interaction of some strategies makes the way clear for power to determine the outcome, whereas the interaction of other strategies causes wars to be protracted, thus dramatically abridging power’s expected effect on the outcome.
Finally, Mack argues that in a long war the high political vulnerability of the strong actor will eventually force it to quit, regardless of whether it has an authoritarian or democratic regime type. This explains why the weak win. The strategic interaction thesis is a general theory of asymmetric conflict outcomes. It improves on Mack’s pre-theory in three areas. First, relative interests determine relative political vulnerabilities, but in the strategic interaction thesis relative interests are not explained by relative power.
The readiness to bear the cost of a war and the readiness to exact a painful toll from others — is a precondition for succeeding in war’’ (Merom, 2003: 19). The argument reduces to the claim that, in small wars, insensitivity to friendly casualties and a willingness to maximize violence against an opponent are necessary for victory; and that modern democracies are from two related problems: (1) weak actors do not always defend with guerrilla warfare (this limits the generality of Mack’s theory); and (2) some defenders using guerrilla warfare strategy are defeated quickly (this limits his theory’s explanatory power).



