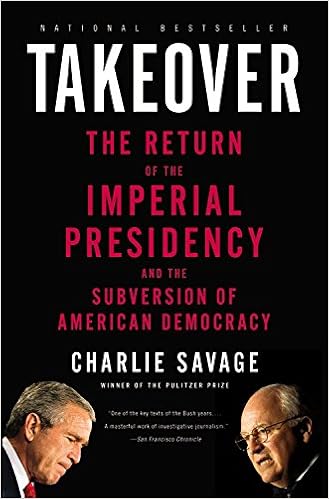
By Charlie Savage
Hailed via liberals and conservatives alike for its revelation of an rising risk to the exams and balances devised by means of our Founding Fathers, Takeover is a searing research into how a gaggle of actual believers, led through Dick Cheney, has seized immense powers for the presidency – and completely altered the constitutional stability of yankee democracy.
Takeover unveils the machinations at the back of the headlines, explaining the hyperlinks among warrantless wiretapping and up to date splendid court docket nominees, among the remarkable politicization of the Justice division and the torture debate, among the White House’s use of “signing statements” and its efforts to impose larger keep an eye on over JAG attorneys. For a person who cares approximately America’s earlier, current, and destiny, Takeover is key examining.
Read or Download Takeover: The Return of the Imperial Presidency and the Subversion of American Democracy PDF
Similar security books
Filenote: mobi made out of retail epub utilizing cloudconvert. org
------------
Good sturdy recommendation and nice concepts in getting ready for and passing the qualified info structures safeguard specialist administration (CISSP-ISSMP) examination, getting interviews and touchdown the qualified info platforms protection specialist administration (CISSP-ISSMP) activity. in case you have ready for the qualified info structures safeguard expert administration (CISSP-ISSMP) examination - now could be the instant to get this e-book and get ready for passing the examination and the way to discover and land a qualified info platforms protection expert administration (CISSP-ISSMP) task, there's totally not anything that isn't completely lined within the ebook.
It is easy, and does a very good task of explaining a few complicated subject matters. there's no cause to take a position in the other fabrics to discover and land a professional info structures safety specialist administration (CISSP-ISSMP) qualified task. The plan is beautiful basic, purchase this booklet, learn it, do the perform questions, get the job.
This publication figures out how you can boil down serious examination and task touchdown options into actual international functions and situations. Which makes this ebook simple, interactive, and worthy as a source lengthy after scholars move the examination. those that train qualified info structures safety specialist administration (CISSP-ISSMP) sessions for a residing or for his or her businesses comprehend the real price of this publication. you actually will too.
To organize for the examination this ebook tells you:
- What you want to learn about the qualified info platforms safety expert administration (CISSP-ISSMP) Certification and exam
- education counsel for passing the qualified info platforms protection expert administration (CISSP-ISSMP) Certification Exam
- Taking tests
The ebook comprises a number of feedback on how getting ready your self for an interview. this is often a side that many of us underestimate, when having a well-written CV, a private web publication, and doubtless a few previous tasks is definitively vital - there's even more to organize for. It covers non-technical facets (how to discover a task, resume, behavioral and so on. ). A 'Must-study' sooner than taking a Tech Interview.
To Land the task, it provides the hands-on and how-to’s perception on
- discovering possibilities - the simplest areas to discover them
- Writing Unbeatable Resumes and canopy Letters
- Acing the Interview
- what to anticipate From Recruiters
- How employers hunt for Job-hunters. .. . and More
This booklet deals first-class, insightful recommendation for everybody from entry-level to senior pros. not one of the different such occupation publications examine with this one.
It sticks out simply because it:
- Explains how the folk doing the hiring imagine, for you to win them over on paper after which on your interview
- is stuffed with invaluable work-sheets
- Explains each step of the job-hunting procedure - from little-known methods for locating openings to getting forward at the job
This e-book covers every little thing. no matter if you try to get your first qualified details platforms defense specialist administration (CISSP-ISSMP) task or stream up within the procedure, you can be happy you were given this book.
For any IT expert who aspires to land a qualified info structures protection expert administration (CISSP-ISSMP) qualified task at best tech businesses, the major talents which are an absolute should have are having an organization snatch on qualified details structures defense expert administration (CISSP-ISSMP) This e-book is not just a compendium of most crucial subject matters in your qualified details platforms defense specialist administration (CISSP-ISSMP) examination and the way to cross it, it additionally can provide an interviewer's standpoint and it covers facets like gentle abilities that almost all IT pros forget about or are blind to, and this publication definitely is helping patch them.
When if you get this publication? even if you're looking for a task or no longer, the answer's now.
Peer-To-Peer Storage: Security and Protocols
Peer-to-peer (P2P) has confirmed as a so much profitable option to produce huge scale, trustworthy, and cost-efficient functions, as illustrated for dossier sharing or VoIP. P2P garage is an rising box of program which permits friends to jointly leverage their assets in the direction of making sure the reliability and availability of person information.
This quantity gathers the papers provided at 3 workshops which are embedded within the IFIP/Sec convention in 2004, to enlighten particular issues which are presently rather lively in safety. the 1st one is the tenth IFIP Annual operating convention on info safety administration. it's prepared by way of the IFIP WG eleven.
- Optical Imaging Sensors and Systems for Homeland Security Applications
- Security and Privacy in Mobile Information and Communication Systems: Third International ICST Conference, MobiSec 2011, Aalborg, Denmark, May 17-19, 2011, Revised Selected Papers
- Global Security Concerns - Anticipating the Twenty-First Century
- Information Security: Principles and Practice
Extra resources for Takeover: The Return of the Imperial Presidency and the Subversion of American Democracy
Example text
Bei Prüfungen im Auftrag des Unternehmens wird häufig externer Expertenrat gesucht, um entweder die Unabhängigkeit zu manifestieren, oder Knowhow zu nutzen, das im Unternehmen nicht verfügbar ist. Eine Prüfung im Auftrag des Unternehmens ist aber auch eine bestellte Wirtschaftsprüfung, die immer stärker auch die IS fokussiert. Diese externen Prüfer müssen durch das Security Management unterstützt werden, wobei das Security Management ebenfalls auf die Einhaltung der festgelegten Maßnahmen durch diese externen Prüfer zu achten hat.
Folgende Fragestellungen müssen beantwortet werden: x Was sind die SLR for Security des Kunden? x Welche Maßnahmen aus dem Service-Katalog eignen sich, um diese SLR for Security zu erreichen? x Welche zusätzlichen Maßnahmen müssen getroffen werden, um diese SLR for Security zu erreichen? x Welche UC werden benötigt, um die SLR for Security einzuhalten? x Welches sind die Pflichten, die der Kunde erfüllen muss? Beispielhaft sei hier wiederum die „sichere Entsorgung von alten Datenträgern“ genannt.
1. Security Manager werden sehr häufig in Stabstellen organisiert. Das liegt einerseits daran, dass dieses eine gängige Position für Datenschutzbeauftragte ist, die nicht selten auch die Funktion des Security Managers übernehmen. Die Position spiegelt aber auch das klassische Verständnis dieser Rolle wieder. Nahe am Vorstand sorgt der Security Manager für ein hohes Maß an Transparenz und Informationsfluss gegenüber der Unternehmensleitung - manchmal aber auch für ein ruhiges Gewissen bei der Unternehmensleitung, dass alles für die IS getan worden ist.



